包阅导读总结
1. 关键词:网络安全、威胁演变、主动防御、协作、未来趋势
2. 总结:本文探讨了在数字化时代,网络安全面临不断变化的威胁,包括更狡猾的攻击、针对关键系统的攻击等。强调了主动防御策略、各方协作的重要性,并展望了未来网络安全的趋势,指出需保持警惕和适应。
3. 主要内容:
– 网络安全的背景:数字时代带来进步也带来新威胁,网络安全至关重要
– 威胁演变:
– 攻击更狡猾,如勒索软件、供应链攻击
– 关键系统受攻击,如电力和交通
– 欺骗手段,如社会工程和钓鱼
– 新兴技术带来新漏洞
– 主动防御的需求:
– 持续评估和修复漏洞
– 构建安全架构和访问控制
– 员工教育和培训
– 利用安全工具和技术
– 协作的重要性:政府、企业和个人需合作,共享情报和最佳实践
– 未来趋势:
– 攻击和防御的自动化
– 量子计算对加密的影响
– 持续创新安全解决方案
– 结论:网络安全是持续战斗,需主动策略、协作和创新
思维导图: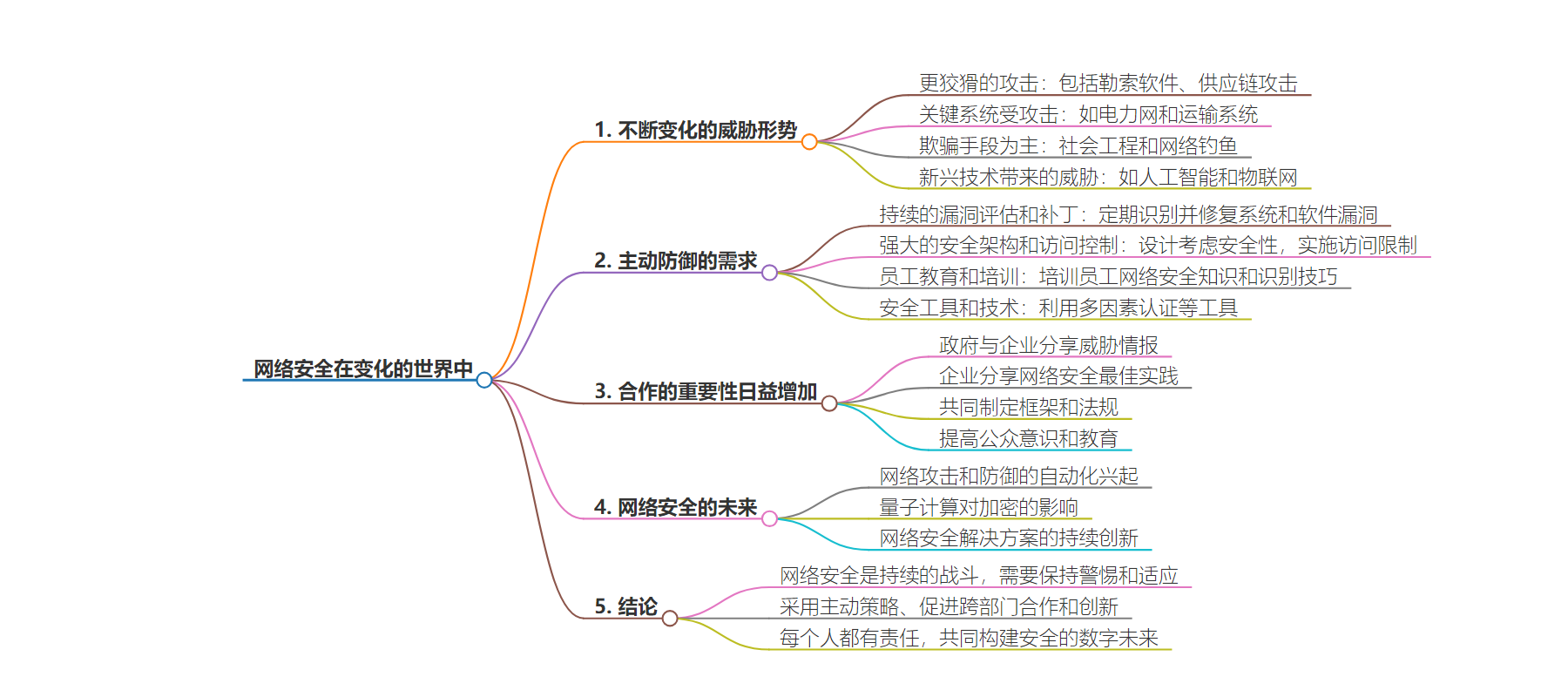
文章地址:https://www.javacodegeeks.com/2024/07/cybersecurity-in-a-changing-world.html
文章来源:javacodegeeks.com
作者:Eleftheria Drosopoulou
发布时间:2024/7/10 12:29
语言:英文
总字数:828字
预计阅读时间:4分钟
评分:82分
标签:网络安全,威胁格局,主动防御,协作,新兴技术
以下为原文内容
本内容来源于用户推荐转载,旨在分享知识与观点,如有侵权请联系删除 联系邮箱 media@ilingban.com
The digital age has brought us incredible advancements, but it has also introduced new and ever-evolving threats. Our growing reliance on technology creates a vast attack surface for malicious actors, making cybersecurity a constant and critical concern. This article delves into the rapidly changing landscape of cybersecurity, exploring the emerging threats, the evolving strategies for defense, and the importance of staying vigilant in this ever-shifting digital terrain.
1. The Evolving Threat Landscape
The world of cyber threats is constantly on the move, like a chameleon changing colors. Just when we think we’ve got things figured out, new tactics and targets emerge. Here are some of the ways cyber threats are evolving:
- More Cunning Attacks: Hackers are getting craftier, developing complex attacks like ransomware that can lock down your entire computer system and demand a ransom to unlock it. Supply chain attacks are also on the rise, where attackers target a trusted supplier to gain access to a larger network. Imagine a hacker infiltrating a software company to infect updates with malware that spreads to all the company’s customers!
- Critical Systems Under Fire: Our reliance on technology means things like power grids and transportation systems are becoming increasingly attractive targets for cyberattacks. A successful attack could disrupt essential services, causing chaos and potential danger.
- Deception is King: Social engineering and phishing tactics are still some of the most common ways attackers gain access to our information. These tricks play on our trust and emotions, tricking us into clicking on malicious links or revealing sensitive data. Phishing emails can look like they’re from a legitimate source, making them even more deceptive.
- Emerging Tech, Emerging Threats: New technologies like artificial intelligence and the Internet of Things (IoT) offer amazing possibilities, but they also create new vulnerabilities. Hackers could potentially use AI to automate attacks or exploit weaknesses in connected devices like smart TVs or thermostats. It’s important to be aware of these potential risks as technology continues to evolve.
2. The Need for Proactive Defense
The ever-evolving threat landscape demands a shift from simply reacting to cyberattacks to proactively preventing them. Here’s a breakdown of key strategies to build a robust cybersecurity posture:
| Strategy | Description |
|---|---|
| Continuous Vulnerability Assessment and Patching | Regularly identify weaknesses in systems and software. Promptly apply updates (patches) to fix these vulnerabilities before attackers can exploit them. |
| Robust Security Architecture and Access Controls | Design your IT infrastructure with security in mind. Implement strong access controls to limit who can access sensitive data and systems. |
| Employee Education and Training | Empower your employees to be the first line of defense. Train them on cyber hygiene practices like password security and recognizing phishing attempts. |
| Security Tools and Technologies | Utilize security tools like multi-factor authentication (MFA) which adds an extra layer of verification during logins. Endpoint protection software actively monitors devices for threats. |
3. The Increasing Importance of Collaboration
The fight against cybercrime is a collective effort. No single entity, whether government, business, or individual, can tackle this ever-evolving challenge alone. Collaboration is key to building a more secure digital landscape. Governments can share vital threat intelligence with businesses, allowing them to identify and defend against emerging attacks. Businesses, in turn, can share best practices for cybersecurity measures, raising the overall level of protection.
Furthermore, developing joint cybersecurity frameworks and regulations can establish a baseline standard for everyone to follow. Finally, fostering public awareness and education on cyber threats empowers individuals to be vigilant and make informed decisions online. This collaborative approach, where everyone plays a part, is crucial in safeguarding our digital world.
4. The Future of Cybersecurity
As technology continues to advance, so too will the tactics used by cybercriminals. Here’s a glimpse into some potential future trends and challenges that security professionals need to prepare for:
| Trend/Challenge | Description |
|---|---|
| Rise of Automation in Cyberattacks and Defenses | Both attackers and defenders are likely to leverage automation. Hackers may employ AI-powered tools to identify and exploit vulnerabilities at scale, while security systems could use automation to detect and respond to threats more efficiently. |
| Impact of Quantum Computing on Encryption | The rise of quantum computing poses a significant threat to current encryption standards. These powerful machines could potentially crack the codes that safeguard our data. New encryption methods resistant to quantum computing will need to be developed. |
| Continuous Innovation in Cybersecurity Solutions | The cybersecurity arms race is a constant one. As attackers develop new techniques, security solutions must evolve to stay ahead. Continuous innovation in areas like threat detection, incident response, and security tools will be critical for maintaining a strong defense. |
5. Conclusion
In conclusion, cybersecurity is a never-ending battle demanding constant vigilance and adaptation. By employing proactive strategies, fostering collaboration across sectors, and embracing innovation, we can build a more secure digital future. Remember, everyone has a role to play – from individuals practicing good cyber hygiene to governments and businesses prioritizing robust defenses. Let’s work together to navigate the ever-shifting sands of cybersecurity and safeguard our digital world.
